Getting connected to Wi-Fi in public spaces has always been a problem, but it’s not just public wifi. Captive Portals, 802.1X, PSK, why can’t there be an easier way to connect to Wi-Fi in a secure fashion that is fast, free, and frictionless while still providing a level of security that’s better than nothing? With over 4 billion Wi-Fi devices hitting the market every year, there is a real need to provide a method of connectivity for devices in a way that rivals the ease of connecting our cellular devices to the LTE network.
Is this lack of an easy way to connect really a problem you ask. Have you ever been on the phone and lost the call when you walked into a building where cellular coverage didn’t exist? Of course. The typical transition time between an LTE & Wi-Fi network is approximately 6 seconds, which has been proven to be the same duration of time that a user will wait before hanging up when they lose the person on the other end of the call. If your device had been able to connect to the public Wi-Fi without user interaction, by way of utilizing multipath, that drop might have been able to be avoided. Cisco thinks that it has the answer to this connectivity problem with their new technology initiative known as #OpenRoaming.
Now if you’re a fan of The Contention Window podcast, you’ll recall that we recently did an episode with some of our Cisco friends talking about what OpenRoaming is & the basics of how it operates. Let’s go into a bit more detail about how this works to help users everywhere.
Check out The Contention Window podcast Episode 10 on Cisco OpenRoaming! http://contentionwindow.libsyn.com/s1e10-aerohive-acquisition-cisco-openroaming
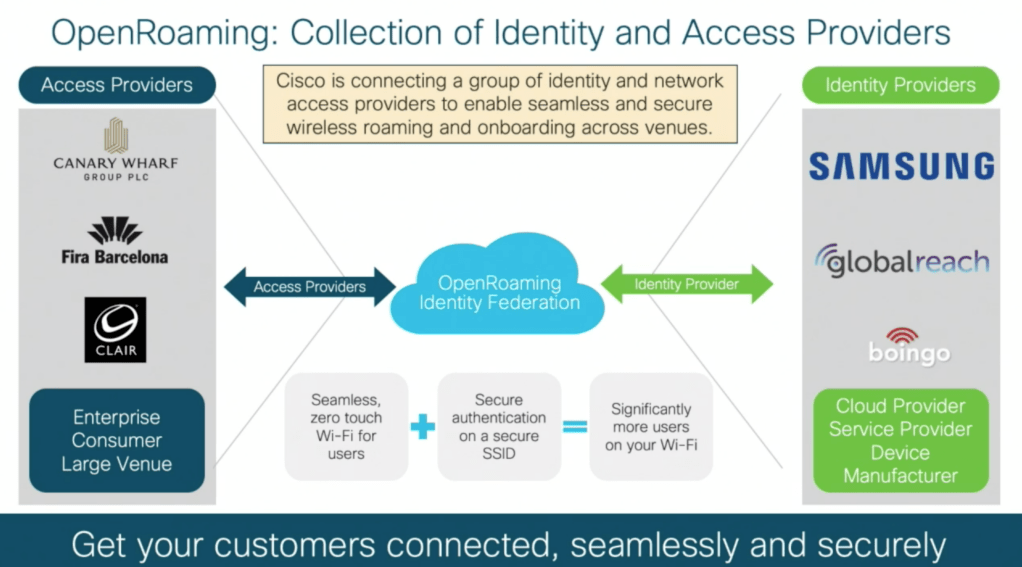
OpenRoaming has 3 components: Access Provider, Identity Federation, and Identity Provider. By tying these groups together, the ability to easily onboard new devices to the network seamlessly occurs. For example, a Samsung device comes with a built in credential (that barring other credentials present on the device) can be utilized to authenticate that device onto the network.
So how does it work at a very nerdy level? Glad you asked!
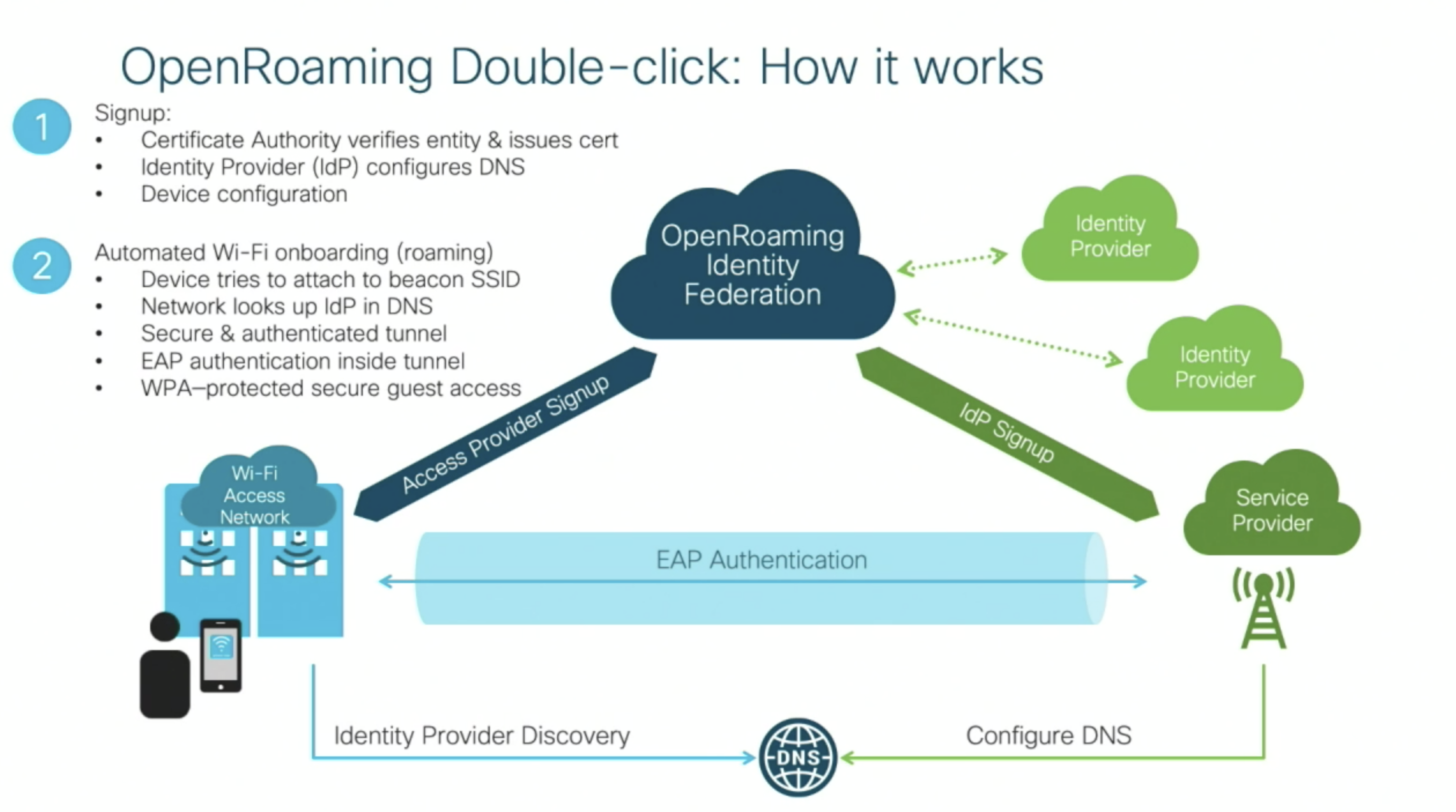
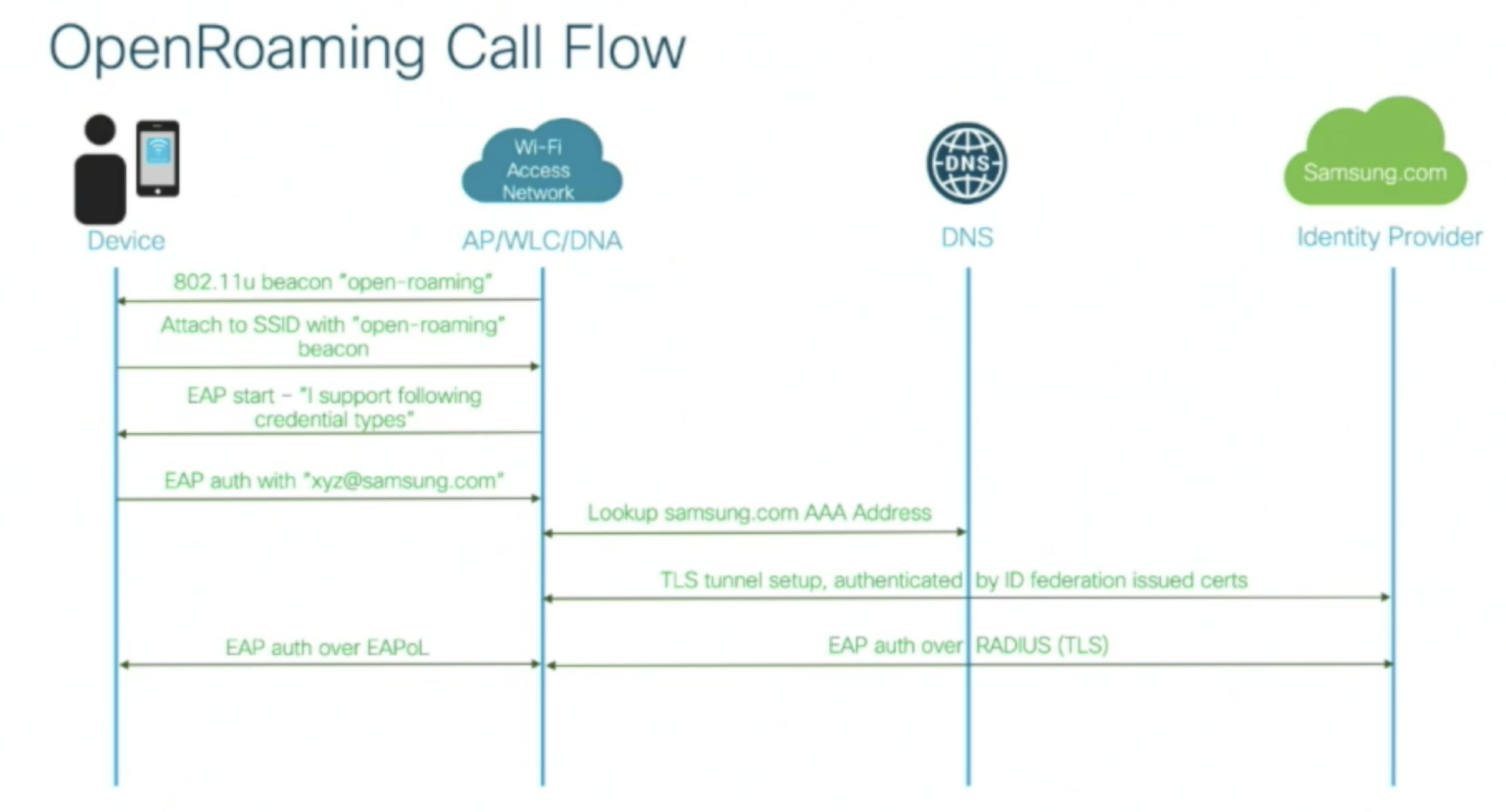
By utilizing .11u, and features that are already compliant with PassPoint, the network is broadcast out and allows devices to connect to the appropriate SSID utilizing the “open-roaming” beacon. After this, the EAP process starts, and uses credentials from the device for the AAA lookup in order to authenticate the device to the Identity Provider that issued the credential.
And that’s it. Well, there are some other nerdy things we could talk about but for sake of this conversation these are the key steps in the process. Cisco started this initiative with the belief that over time, with a bit of help fostering the development and building relationships with other companies interested in maintaining this federation long term, OpenRoaming could create an environment where our devices are essentially always connected. While I’m sure that eventually we shall see this process monetized in some way, hopefully we see it done in a way much like cellular roaming occurs today. Where the fees are somewhat invisible to the end user, and all you know is that your call works regardless of what state or city you might be located in.
Keep in mind that Rome wasn’t built in a day, and PassPoint support is still somewhat limited across the globe, but maybe over time we will see this take hold as something commonplace in the Wi-Fi world. OpenRoaming is launching early 2020 so keep an eye out. We’ll see what happens and how quickly the possibility of this initiative takes hold.
If you want to check out the full video from #MFD4 about Cisco OpenRoaming, check it out here!
Cisco OpenRoaming to Better Bridge Between Mobile and Wi-Fi Networks from Gestalt IT on Vimeo.
-Scott









Pingback: A New Way to Onboard - Tech Field Day
Pingback: Wi-Fi is dead? Continued | The it Rebel
Pingback: CTS 184: Cisco @ Mobility Field Day 4