Accessing the network – Part Two
We left off Part One in our series, asking how organizations could leverage their existing investments in a wireless network to bridge the gap of indoor coverage left by cellular technology. Let’s face it. While CBRS might be useful, the expenses of yet another overlay network aren’t something that can be taken lightly. In fact, some of these overlay networks may result in 2-3x the costs associated with the existing WLAN infrastructure already in place.
So what can an organization do?
Back in 2012, Passpoint was created and designed as easy way to onboard devices to wireless networks, initially utilizing SIM (Subscriber Identity Module) cards to provide the credentials needed to authenticate a device to the network. For most of the major carriers, participating in Passpoint has not been something they have shied away from (here’s looking at you Verizon) but they have embraced as a way to easily offload data traffic to supported wireless networks. This has effectively helped them stretch the capacity of the cellular network by freeing up resources, much in the same way a wireless engineer follows the motto of “if it doesn’t move, wire it”. With no cellular carrier prohibited from utilizing Passpoint, do we really need a new way to onboard?
In a previous post, I discussed a new way of onboarding devices to wifi that was designed to provide the same ease of connectivity that our cell phones have to the cellular network today. (You can read that post here.)

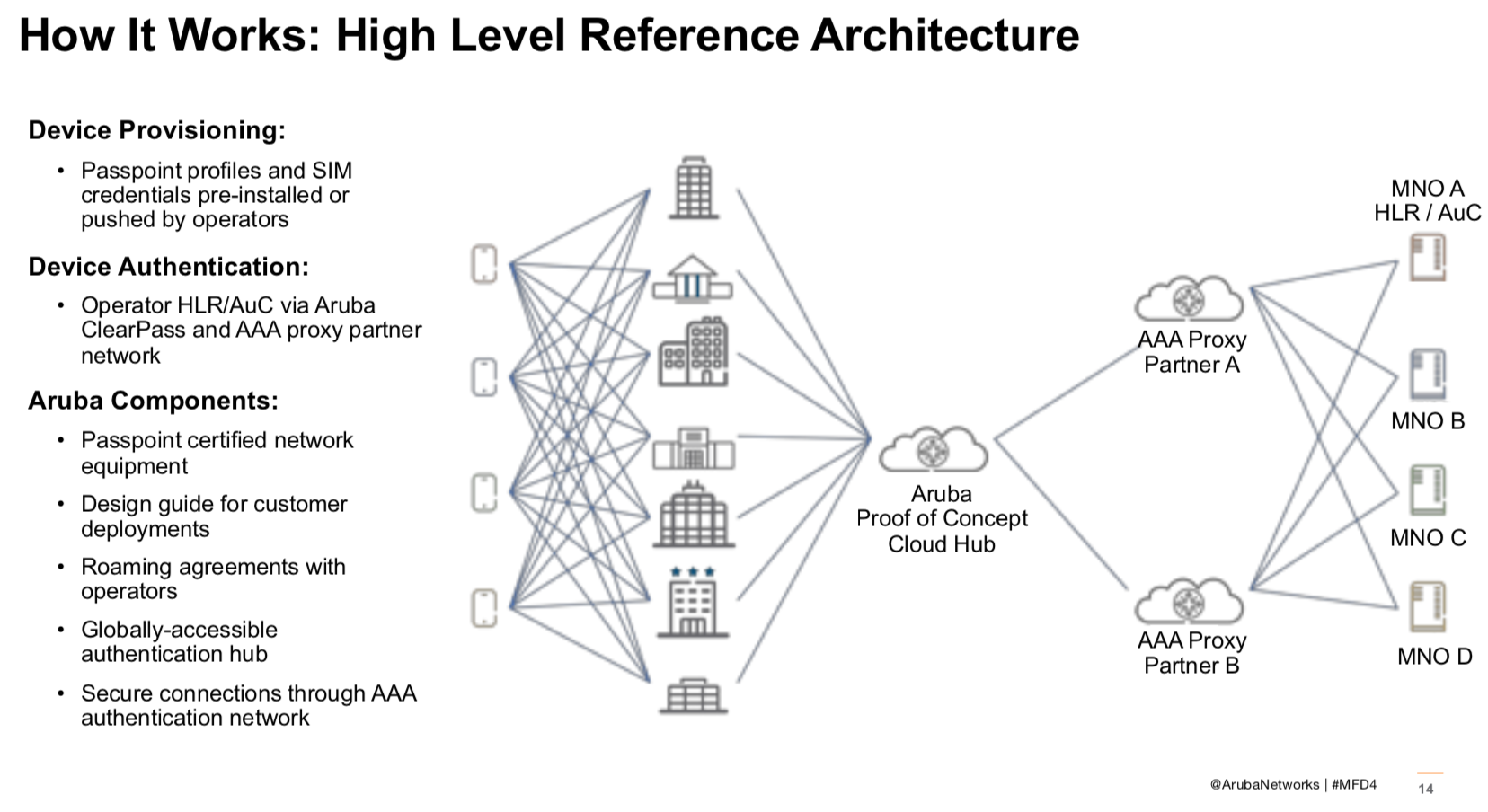
So what’s involved in getting Passpoint to authenticate you ask? If you reference the image above, there is an addendum to the standard SSID beacon that notifies devices that the network is Passpoint/HS 2.0 compatible (802.11u). Once the device sees this, the device attempts to use its internal credentials (ex. SIM card info) to connect and authenticate to the wireless network using EAP just as a 802.1X connection does. Unbeknownst to most network administrators, there is no provision that excludes non-SIM enabled devices from utilizing the Passpoint service to connect a device. If we take a look at the graphic below, you can see the reference architecture for how Aruba believes they can help solve the device authentication issue as a type of broker if you will. Aruba intends on becoming the authentication broker, thus forming the roaming agreements with the various operators (MNOs – mobile network operators), in order to remove some of the hurdles that are presently in place from truly making Passpoint something easily deployed by end users.
Well that’s all great, but can Passpoint really deliver on being a primary form of connectivity to the WLAN? Aruba thought so, and the testing they’ve done helps prove their point that in fact, it can be.
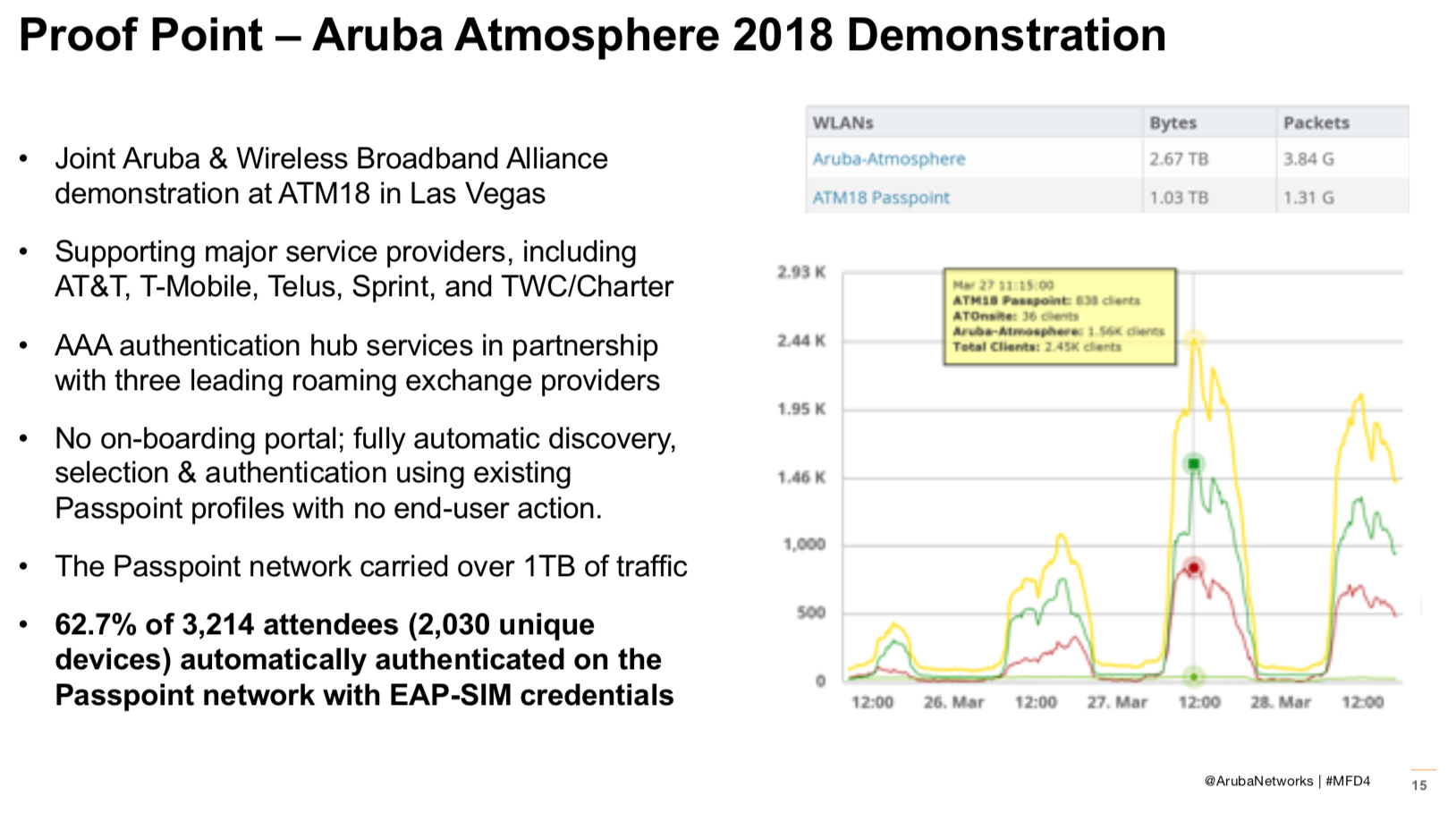
As you see in the graphic above, Aruba decided that for the 2018 Atmosphere conference they would run the conference network with Passpoint enabled. The goal was simple. Show that a secure network can easily onboard users, and by easily we mean with little/no interaction from the end user, and provide a good user experience. Having attended the conference, I can say that this was a resounding success in my opinion. As an AT&T user, the experience worked very well for me without requiring any additional effort to connect to the WLAN. I simply walked into the conference area, and done! It worked that well for over 62% of the conference attendees as well based on the information provided by Aruba. And to take it a step further, Aruba even runs this same network configuration in their HQ out in Santa Clara, CA. If you were wondering, while we were there for MFD4, the experience worked as flawlessly for my mobile device as it did in years past at Atmosphere. 😉

So with all of this being said, do we really need ANOTHER new way to onboard users like some other think we do? Maybe. However, the team at Aruba thinks that leveraging the features we already have available can handle that responsibility just fine. All Aruba wants to do is provide a little push to help kick start the process, and bring users onto a secure network while providing an excellent user experience.
For the presentation in it’s entirety, please check out the video from #MFD4 on the topic below!
Aruba Enterprise Passport and the Future of In-Building Coverage from Gestalt IT on Vimeo.









Great blog! Passpoint will be huge for guest Wi-Fi scenarios if Aruba and others can bridge the business roaming agreement gap and act as a broker for federated authentication.
That said, a large part of the anticipated CBRS Private LTE/5G value proposition has nothing to do with guest networks or onboarding issues, rather higher service levels for core business critical applications and processes. Guest onboarding is nice, and necessary, but only a small part.
Further, guest onboard might* alleviate the need / desire for better indoor cellular coverage by carriers (*lots of caveats). But it doesn’t address the desire for private cellular for enterprise control and management. There is a significant CBRS focus outside of carriers, to serve as private networks for enterprises.
Thanks,
Andrew von Nagy
LikeLike
Pingback: Wi-Fi is dead? | The it Rebel
Pingback: Wi-Fi Is Dead? Continued - Tech Field Day
Pingback: CTS 192: Aruba @ Mobility Field Day 4